Real-Time Fraud Detection System with Splunk -
Case Study
Key takeaways
- Fraud detection systems play an important role in preventing cyber threats in financial institutions.
- One of our clients in the financial sector was facing issues in identifying fraud cases quickly.
- After implementing our solution, Splunk Enterprise enabled centralized data analysis and faster fraud detection.
- Detection times have improved significantly, with many cases identified within minutes.
- Early detection helps limit potential financial losses and reduces overall risk exposure.
Introduction
Fraud remains one of the most persistent threats facing financial institutions. In 2024, payment fraud in the European Economic Area was valued at €4.2 billion, marking a 17% increase from the previous year. This poses a serious threat not only to the financial sector but also to people.
As attack methods evolve, banks and other financial organizations must detect suspicious activity faster, investigate it more efficiently, and respond before major losses occur.
In this case study, we describe how we helped a European financial institution strengthen its real-time fraud detection system using Splunk Enterprise. The goal was to improve visibility into suspicious behavior, shorten detection times, and support the fraud team with a more scalable and structured approach to identifying potentially dangerous activity.
The result was a centralized detection approach built around risk scoring, behavioral monitoring, and alerting. By combining multiple sources of data in Splunk, the organization gained a stronger ability to detect suspicious patterns earlier and take action faster.
The challenge - fraud detection
Before this work began, one of the key areas for improvement was the time required to detect potential fraud cases. In some situations, suspicious activity was identified with a delay, which limited the ability to respond as quickly as desired.
The detection process at the time relied on more traditional and partly manual approaches. As a result, follow-up activities required significant effort from employees, and there were limited tools available to support faster analysis and decision-making.
Another major challenge was the data itself. Fraud signals were spread across multiple systems and data sources, each with its own format and structure. That made the analysis more challenging, especially when trying to understand how isolated events might fit into a larger fraud pattern.
Another key consideration was handling a large volume of data. The system needed to process tens of millions of events efficiently and reliably. Without the ability to analyze this volume of data in near real time, detection would remain slower and less consistent than the customer needed.
- centralize fraud-related data
- detect suspicious behavior earlier
- reduce manual effort
- prioritize the highest-risk cases
- support a more resilient fraud response model
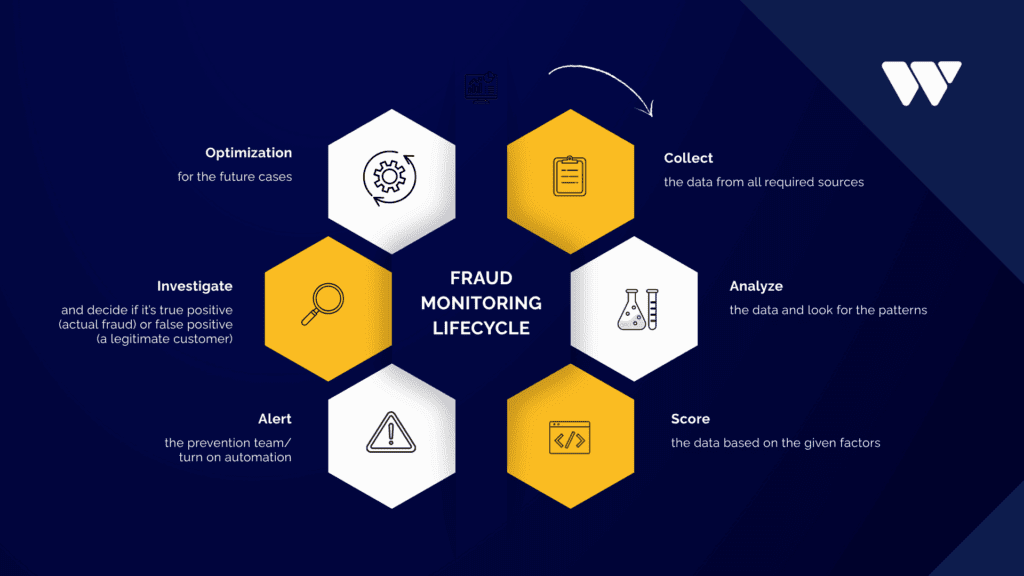
Understanding the fraud scenario
In the digital world, fraud often begins when a customer is tricked into interacting with a malicious message, link, or imitation service that appears legitimate. This may lead to unauthorized access attempts, misuse of customer credentials, or suspicious activity connected to account onboarding, authentication, or payments.
Because these incidents are designed to resemble normal customer behavior, they can be difficult to identify through simple rule-based monitoring alone. The risk is not limited to a single payment or transfer. In many cases, the earlier indicators appear in supporting events such as unusual device activity, unexpected login behavior, or patterns that differ from the customer’s typical usage.
For this reason, effective fraud detection in financial institutions requires a broader view of customer activity. Instead of evaluating events in isolation, detection logic must combine multiple signals and assess them together in context. This makes it possible to identify suspicious behavior earlier and improve the ability to respond before greater damage occurs.
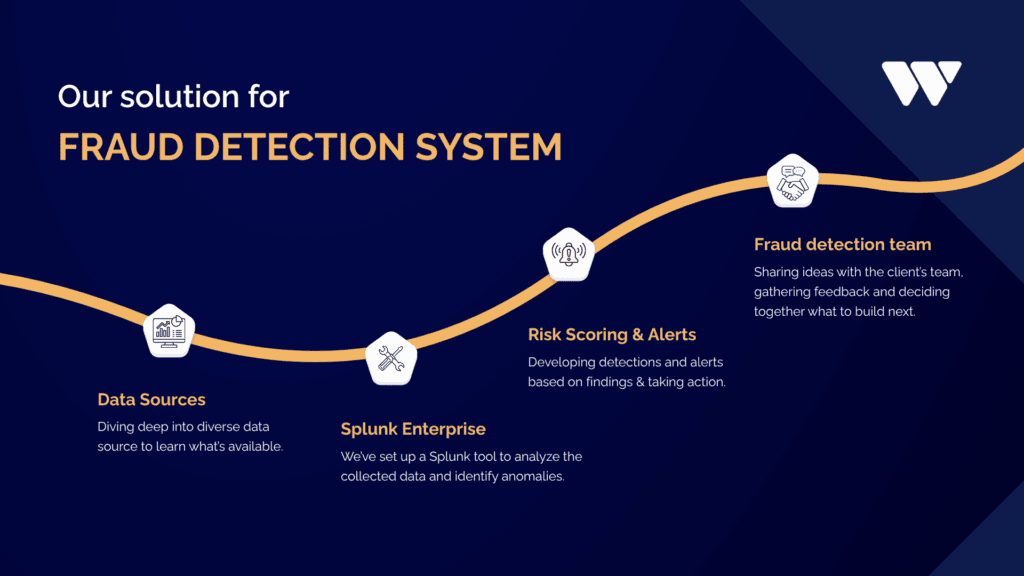
Our Splunk solution
Following an analysis of the client’s requirements and available data sources, we selected Splunk Enterprise as the core technology. As an on-premises solution, it aligns well with the strict data security and compliance requirements typical in the financial sector, while providing a reliable foundation for fraud detection.
The solution uses data from sources such as:
- online events
- mobile application activity
- device-related information
- selected end-user context data
- fraud detection team observations and historical case records
Splunk Enterprise acts as the central platform for ingesting, normalizing, correlating, and analyzing these signals. It is used to calculate risk scores, store detected fraud cases for further analysis, and support the day-to-day work of the fraud detection team.
The overall approach includes multiple detection mechanisms and alerts. Each alert contributes to a broader understanding of customer risk. Instead of relying on a single signal, the solution uses a layered model where different suspicious behaviors increase the overall risk score.
When the score exceeds a defined threshold, an alert is generated and shared with the fraud team and connected external processes. This helps the organization respond faster and, when necessary, apply protective actions such as restricting payment activity or escalating the case for investigation.
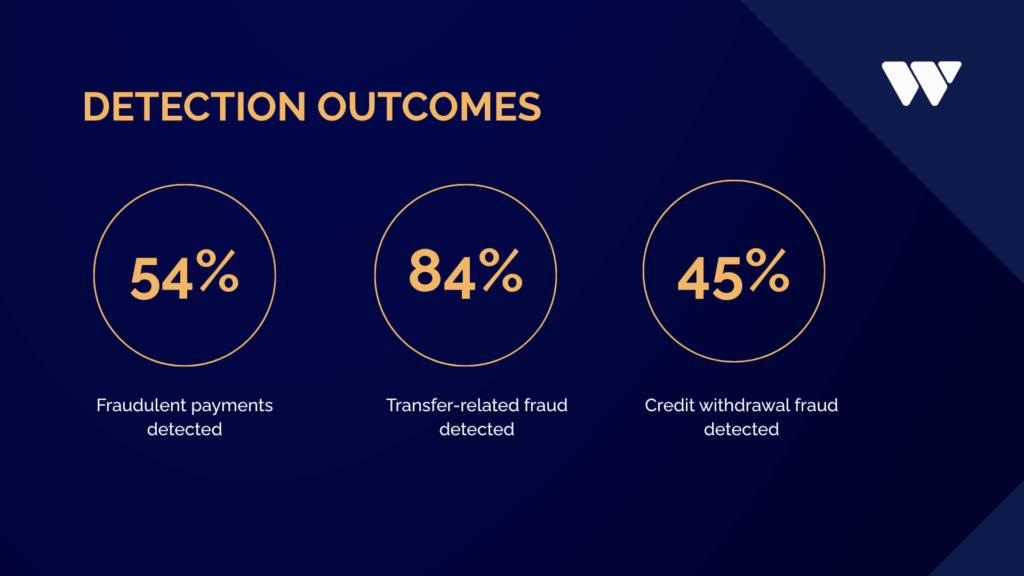
The Results
One of the most significant benefits of the solution has been its financial impact. Fraud cases can vary widely in severity, from relatively minor incidents to substantial losses. Detecting suspicious behavior earlier helps reduce the likelihood that damage will escalate and supports more timely intervention.
Detection speed has improved considerably. In many cases, suspicious activity can now be identified within minutes, with some incidents detected in under 10 minutes. As a result, certain fraud patterns that were previously more common are now observed less frequently. At the same time, fraud methods continue to evolve, requiring ongoing adjustments to detection approaches.
Importantly, these results were achieved in less than six months from the start of the project, beginning from a completely new foundation. Development is still ongoing, but the progress already made shows the value of a focused and structured approach to fraud detection.
Currently, the system can identify around:
- 54% of fraudulent payments
- 84% of money transfer-related fraud cases
- 45% of credit withdrawal fraud cases
Thanks to the implementation of the system, the company was better able to detect unauthorized payments, transfer-related fraud, and credit card withdrawals. This reduced the workload of department staff and enabled more accurate analysis of potential future incidents.
The team can now work faster and focus more effectively on the most important matters, and our client can make conclusions and carry out the necessary reporting regarding fraudulent actions.
These results were achieved using Splunk Enterprise for behavioral analysis, centralized monitoring, and risk-based scoring.
Why Splunk was a good fit
Splunk was a strong fit for this use case because fraud detection depends heavily on bringing together data from multiple environments and making sense of it quickly.
For this customer, Splunk provided several important advantages:
| Capability | Why it mattered |
|---|---|
| Centralized data analysis | Allowed the team to combine signals from multiple sources in one place |
| Fast search and correlation | Improved the ability to investigate suspicious behavior quickly |
| Flexible alerting | Supported multiple fraud use cases and detection models |
| Risk scoring support | Helped prioritize the most important cases |
| Historical analysis | Made it easier to compare current behavior with past fraud patterns |
| Scalability | Supported analysis across tens of millions of events |
For a fraud detection system for financial institutions, these capabilities are especially valuable because fraud does not usually happen in a single system. It often emerges through a chain of events across identity, device, login, and transaction activity.
Fraud detection and regulatory resilience
For European financial institutions, fraud detection is not only a security priority but also part of a broader regulatory and operational resilience requirement. Frameworks such as the Digital Operational Resilience Act (DORA) place greater emphasis on risk management, traceability, monitoring, and the ability to detect, respond to, and report incidents in a structured way.
In this context, fraud detection capabilities support more than day-to-day security operations. They also help institutions improve visibility across digital services, strengthen auditability, and build more consistent response processes. Centralized monitoring, retained event data (including archiving), and risk-based analysis all contribute to a more controlled and resilient operating model.
At the same time, technical controls alone are not enough to address every fraud scenario. Some attacks rely heavily on social engineering and user manipulation, which means long-term resilience also depends on customer awareness and continuous adaptation to evolving threats. For that reason, effective fraud prevention requires both strong detection capabilities and an operating model that can develop over time.
Summary
This case study shows how a European financial institution improved its fraud monitoring capability by building a more structured fraud detection approach.
By combining multiple data sources and using Splunk Enterprise as a centralized analysis platform, the organization improved fraud visibility, accelerated detection, and supported more consistent case handling. Risk scoring, behavioral monitoring, and historical device analysis helped the fraud team prioritize suspicious activity and respond faster.
As fraud techniques continue to change, the ability to adapt detection logic over time is essential. A flexible, data-driven approach makes that possible. For financial institutions, the value is clear: faster detection, better visibility, reduced manual effort, and stronger support for operational resilience.
About WeAre Solutions Oy
WeAre Solutions Oy is a Finnish observability-focused consultancy and a leading Splunk Elite Partner in the Nordics. We specialize in observability and monitoring (using Splunk), Atlassian services (Jira), and software development. Founded in 2016 and headquartered in Helsinki, our mission is to turn observability into a competitive advantage for organizations.
At WeAre, we help organizations assess their Splunk environments, identify improvement opportunities, and align performance with real business needs. You can start with an observability assessment to understand your current state, or contact our team for a free consultation.
